Introduction to IoT Security
- Post by: Anca Delia Jurcut, Pasika Ranaweera and Lina Xu
- September 5, 2019
- Comments off
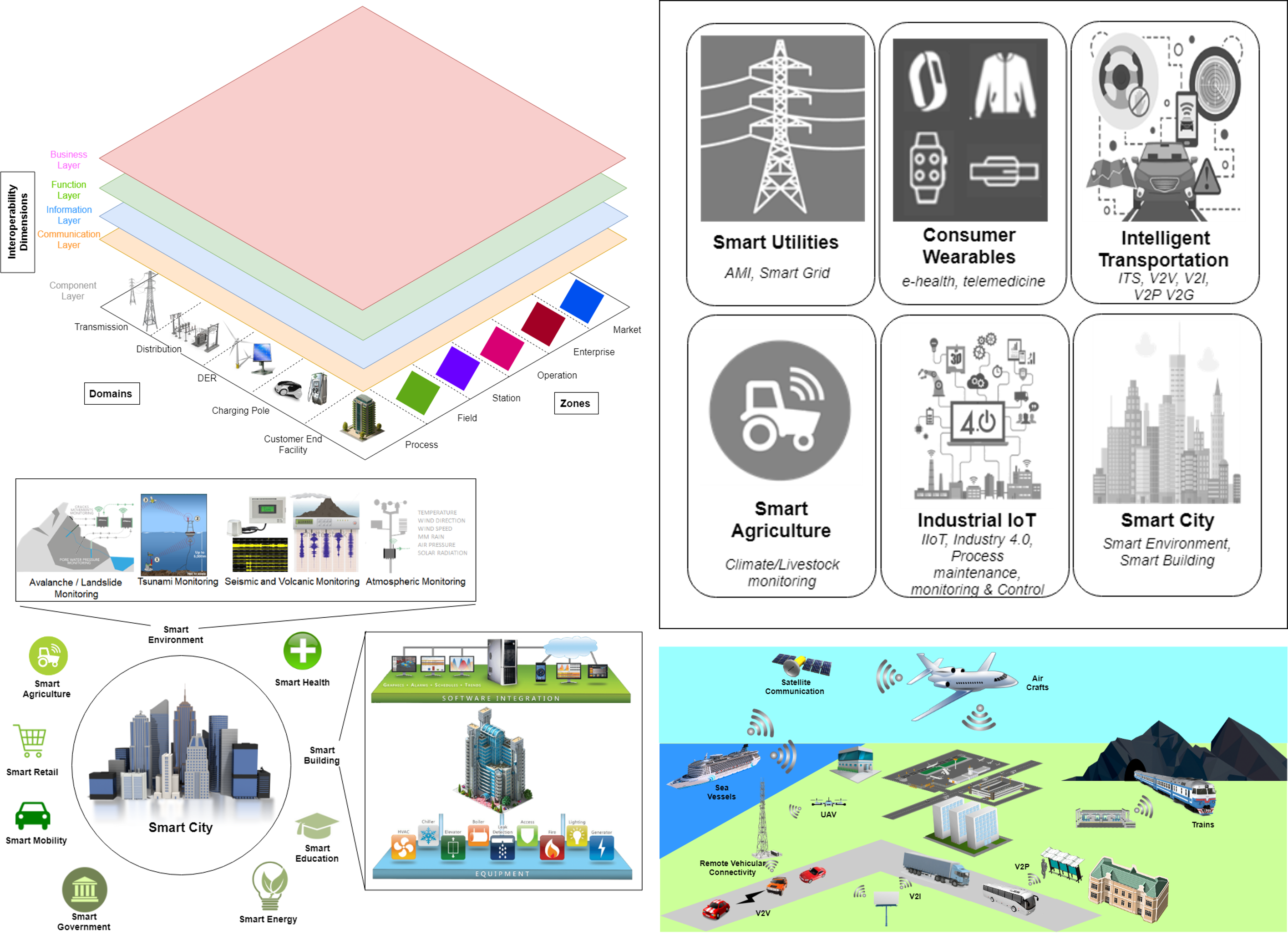
In a world with “things” and devices interconnected at every level, from wearables to home and building automation, to smart cities and infrastructure, to smart industries, and to smart everything, the Internet of Things (IoT) security plays a centric role with no margin for error or shortage on supply. Securing, including the authentication of these devices, will become everyone’s priority, from manufacturers to silicon vendors (or IP developers), to software and application developers, and to the final consumer, the beneficiary of the security “recipe” that will accompany these IoT products. Together, they need to adapt to the market demands, innovate and improve processes, grasp new skills and learn new methods, raise awareness, and elaborate new training and curricula programs.
In this chapter, we provide a thorough survey and classification of the existing vulnerabilities,
exploitable attacks, possible countermeasures, and access control mechanisms, including
authentication and authorization. These challenges are addressed in detail, considering both the
technologies and the architecture used. Further, this work focuses also on IoT intrinsic vulnerabilities as
well as the security challenges at every layer. Additionally, solutions for remediation of the
compromised security, as well as methods for risk mitigation, with prevention and improvement
suggestions are discussed.

Pasika Ranaweera is an Assistant Professor in the School of Electrical and Electronic Engineering in University College Dublin from September 2023. He was a Post-Doctoral Researcher in the UCD School of Computer Science in 2023. He was the project manager of the CONFIDENTIAL-6G project, funded by the EU H2022-SNS grant id: 101096435, during this profession. He obtained his Bachelor's degree in Electrical and Information Engineering from the Faculty of Engineering, University of Ruhuna, Sri Lanka, in 2010 with honors and received the Lanekassen scholarship for pursuing the Master’s Degree in Information and Communication Technology (ICT) in 2013 from the University of Agder, Norway. Pasika completed his Ph.D. from University College Dublin, Ireland, on improving the security of service migrations of MEC in 2023. Prior to his Ph.D., he served as a lecturer attached to the Department of Electrical and Information Engineering, Faculty of Engineering, University of Ruhuna, Sri Lanka, from 2014 to 2018. Pasika is experienced in conducting teaching/ instructing/ demonstration work at international universities (UCD-Ireland, BDIC-China). He is currently conducting collaborative research with researchers at IIT-India, the University of Oulu-Finland, and the University of Ruhuna-Sri Lanka. Pasika is focused on enhancing the security measures in 5G and beyond 5G mobile networks, while his main research focus is directed at Federated Learning-based security issues and how to overcome them utilizing Blockchain. His additional research directives extend to lightweight security protocols, formal verification, security, service quality optimization, 5G and MEC integration technologies (SDN, NFV, Blockchain), privacy preservation techniques, and IoT security. In addition to the research work, he serves as a reviewer for IEEE IoT journal, IEEE Access, IEEE Communication Magazine, IEEE IoT Magazine, SN Computer Science, and various IEEE-hosted conferences and workshops under the IEEE Communication Society (also a member of IEEE ComSoc).