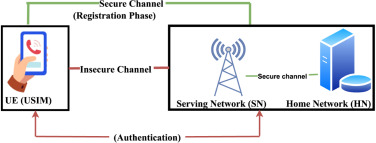
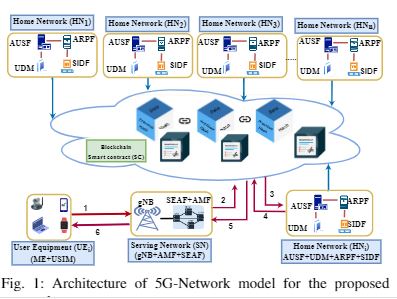
Multi-Access Edge Computing (MEC) is a novel edge computing paradigm that enhances the access level capacity of mobile networks by shifting the serviceable Data center infrastructure proximate to the end devices. With this proximate placement and service provisioning, migration of a service from one edge enabled gNodeB (gNB) to another is intrinsic to maintain the […]
Read More
Service Migration Authentication Protocol for MEC
- December 7, 2022
- Comments off